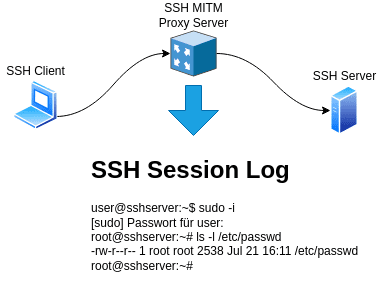
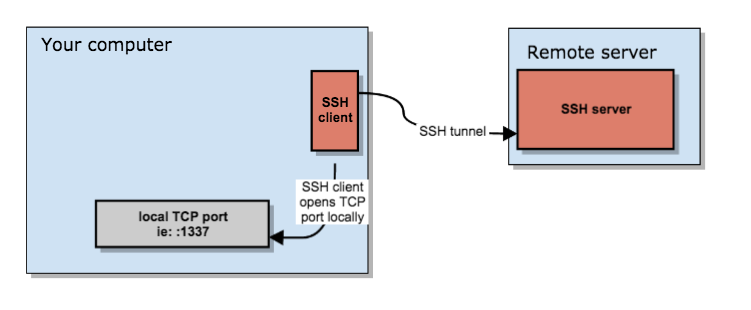
Offensive Security Guide to SSH Tunnels and Proxies | by Russel Van Tuyl | Posts By SpecterOps Team Members
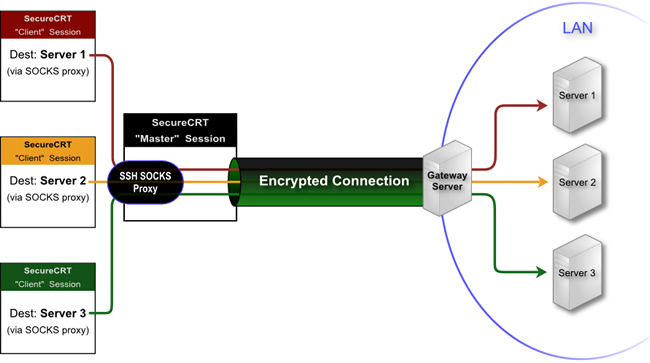
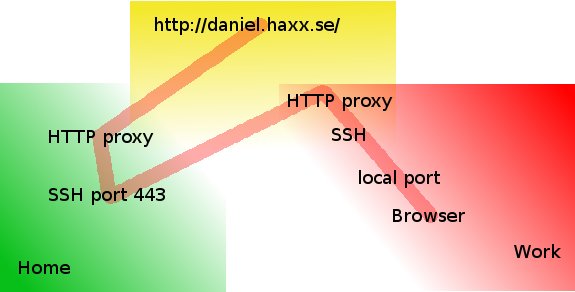
Howto Pass SSH traffic through a Secured Corporate Proxy server with corkscrew, using sshd as a standalone proxy service with no proxy installed on remote Linux server or VPS - ☩ Walking
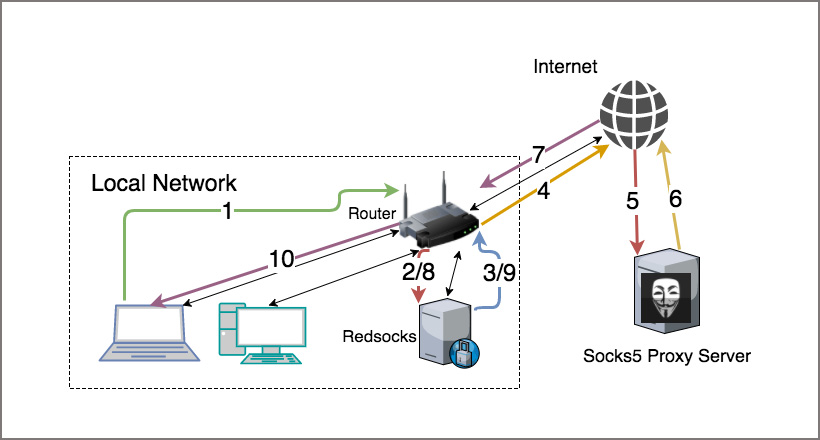
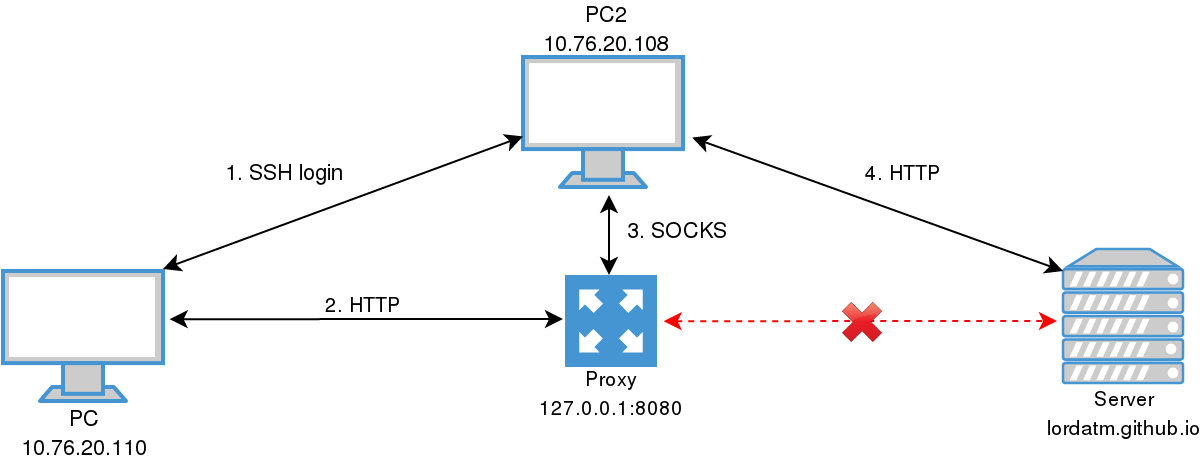
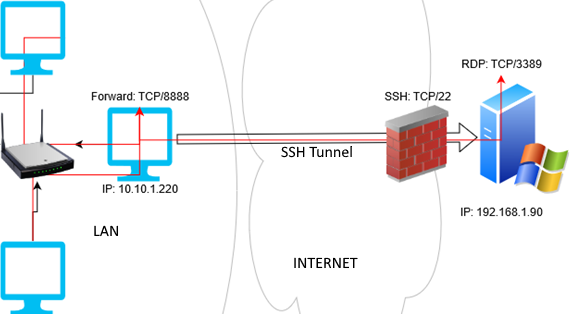
How to Route All Network Traffic from your LAN securely through a SOCKS5 proxy + SSH Tunnel + Redsocks | DNSFLEX